Problems pile up for LayerZero amid fresh memecoin trading accusations
LayerZero, a cross-chain messaging platform, is facing new accusations of operations security (OPSEC) failures. According to reports, its production multisig signing keys traded McPepes memecoin on Uniswap.
Per the allegations, which were made public on May 8, 2026, faults were directed to key management techniques used by blockchain infrastructure companies.
What happened with LayerZero’s 2-of-5 Gnosis Safe multisig?
The accusations center on reckless use of LayerZero’s 2-of-5 Gnosis Safe multisig, a method by which they secure their users’ tokens and control key parts of their OFT infrastructure.
From screenshots of an internal discussion that went viral on X, three of the five signers of the Gnosis Safe multisig were actively involved in activities unrelated to the multisig process.
Signer addresses include:
- 0x1f5E377a3ADBe6f3289ADb6b21eae6427dfbb553, which is associated with the trading of the memecoin called PEPES (McPepes) and the Hop platform.
- 0xBb6633c267951E938F9B6421E4F54aa5b2c19326, which held approximately $12 million and engaged in Stargate staking.
- 0x6fC8342C448F9a8d541C17579EF7A14237b8d5aD, involved in liquidity provisioning on Curve, PancakeSwap, and SpookySwap.
A notable transaction on March 1, 2023, involved exchanging 0.198548073 ETH for approximately 1.73 million tokens of the ERC-20 token McPepes/PEPES via Uniswap V3.
This has been cited as evidence that the production keys, whose purpose was to safeguard billions of dollars, were linked to websites outside the network, thereby leaving them vulnerable to phishing attacks.
The multisig lacked a timelock, and the keys remained stagnant for several years. The same parties are responsible for the multisig-controlled DVN settings and libraries for LayerZero-compatible protocols.
On-chain transactions support the assertion that the production signers performed Uniswap swaps for the McPepes prior to the PEPE token deployment schedule.
Reported vulnerabilities tied to the multisig setup
The LayerZero multisig was created to serve as the ultimate layer of protection for bridged tokens. Nevertheless, the described actions broke the fundamental OPSEC rule of key isolation. By using the same keys to trade on decentralized exchanges, the signers risked vulnerability to attacks from malicious contracts and phishing schemes.
It is worth mentioning that only two stolen keys were enough to empty the whole multisig.
The timing of the disclosure is associated with increased scrutiny of LayerZero’s security approach. As reported by Cryptopolitan, only hours before that, Solv Protocol revealed its intention to migrate more than $700 million worth of tokenized BTC (SolvBTC and xSolvBTC) to Chainlink’s CCIP from LayerZero.
The company cited updates to security reviews and bridge issues, such as the recent Kelp DAO hack that used LayerZero bridges. Although Solv did not mention this incident in its announcement, it still illustrates a certain degree of skepticism toward LayerZero.
LayerZero’s CEO Bryan Pellegrino speaks on the matter
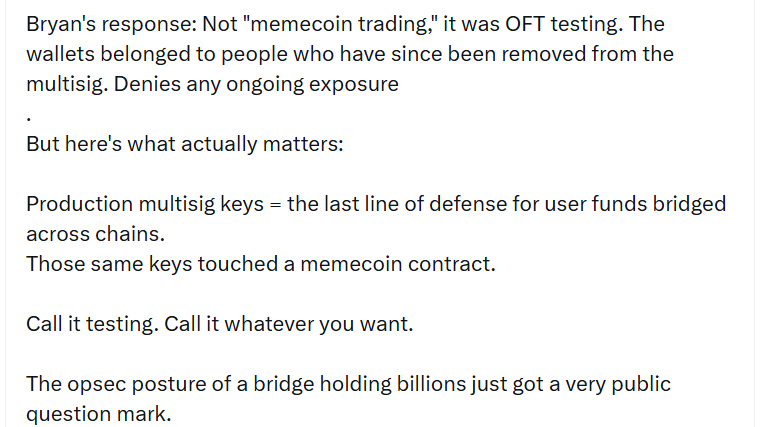
In response to the accusations, LayerZero’s CEO, Bryan Pellegrino, said the transactions originated from former members of the multisig wallet who had been booted out. He denied there was any such thing as “memecoin trading,” saying that it was just OFT testing, not speculations.
Furthermore, he pointed out that the wallets were no longer involved in signatory functions.
 LayerZero CEO Bryan Pellegrino denies accusations. Source: X
LayerZero CEO Bryan Pellegrino denies accusations. Source: X
As shown in the screenshots, skeptics raised issues regarding the description of the incident, citing that the transaction was between McPepes (not PEPE) and raising doubts about how ETH to memecoin trading via Uniswap could be classified as OFT tests.
The signers in question have reportedly been removed from the multi-signature. No counter-rebuttal or full audit of all previous actions carried out by the signers had been made public by LayerZero.
Crypto Twitter goes after LayerZero
Zach Rynes has gone against LayerZero, calling the security measures a “horrific opsec.” Rynes pointed out the dangers posed by such behavior to users running LayerZero in its default settings. He has cited potential supply-chain exploits.
Additionally, he asserts that production keys must never be used for anything other than vital tasks.
X community reactions range from shock at what they perceived as “clowns and criminals” working within the infrastructure domain to a call for more openness and transparency.
Any potential vulnerabilities within the multisig of LayerZero, which acts as an intermediary for chain-to-chain communication, could be very concerning.
The smartest crypto minds already read our newsletter. Want in? Join them.
You May Also Like

CoreWeave (CRWV) Stock Surges 12% on $8.5B GPU-Backed Financing Deal — Here’s the Full Picture

Family offices stall deal-making during Iran conflict






