Fireblocks Exposes Sophisticated Lazarus-Linked Hiring Scam
Fireblocks has disclosed details of a highly coordinated cyber campaign in which North Korean threat actors impersonated the company’s recruiters to target crypto developers with malware. The investigation, published on January 22, 2026, revealed that attackers linked to the Lazarus Group leveraged fake recruitment processes to compromise victims’ systems and steal sensitive digital asset credentials.
The operation, internally labeled Operation Contagious Interview by Fireblocks’ security team, demonstrated a high level of sophistication. Attackers posed as legitimate Fireblocks recruiters on LinkedIn and used realistic hiring workflows to establish credibility before delivering malicious payloads disguised as routine coding tasks.
Impersonation Tactics and Social Engineering
According to the findings, the attackers created multiple convincing LinkedIn profiles that appeared to belong to Fireblocks executives, recruiters, and hiring managers. These profiles included professional photographs, detailed employment histories, and network connections aligned with blockchain and technical roles. Unlike many phishing attempts, the campaign avoided obvious warning signs such as spelling mistakes or poor formatting.
Once developers engaged with these profiles, they were sent professionally designed PDF documents outlining a fictitious initiative referred to as the Fireblocks Poker Platform. To further reinforce authenticity, the attackers built detailed design mockups using tools such as Figma. The materials closely mirrored Fireblocks’ real branding and referenced the company’s recent acquisition of Dynamic, which had been announced only weeks earlier. This level of accuracy indicated that the attackers were actively monitoring Fireblocks’ public announcements.
Fake Interviews and Malware Delivery
The scam extended beyond written communication into live interaction. Victims were invited to video interviews conducted over Google Meet, where the impostors followed standard hiring practices by asking about work experience and compensation expectations. After establishing rapport, the interviewers assigned what was presented as a code review or technical assessment and abruptly ended the call, citing scheduling constraints.
The malicious stage of the attack occurred when candidates followed standard developer workflows. Victims were instructed to clone a GitHub repository and run npm install, a common setup step. Executing this command triggered hidden malicious code, granting attackers access to the victim’s system. The malware infrastructure also employed a technique known as EtherHiding, which uses blockchain smart contracts to host command-and-control instructions, making the operation more resilient to takedowns.
Attribution to the Lazarus Group
Fireblocks’ security research team attributed the campaign to APT 38, a subgroup of the Lazarus Group known for financially motivated cyber operations. The investigation identified similarities with earlier attacks, including a previous recruitment scam that impersonated Multibank Group and used a comparable fake poker platform as bait.
The primary objective of the operation was financial theft. By compromising developers’ machines, the attackers sought to steal credentials, private keys, seed phrases, and access to development environments. Because developers often have elevated access to production systems and sensitive repositories, successful infections could provide attackers with entry points into entire organizations.
Indicators and Campaign Disruption
Fireblocks identified at least twelve fake personas used during the campaign. Indicators of compromise included the use of personal email addresses instead of corporate domains, Calendly links hosted on non-corporate sites, AI-generated profile descriptions, and LinkedIn accounts with little historical activity that suddenly became active.
The campaign began to unravel when several job seekers contacted Fireblocks employees directly to ask about the supposed poker platform project. These inquiries were escalated internally, allowing the security team to confirm the impersonation. Fireblocks then worked with LinkedIn to report and remove fraudulent profiles and coordinated the takedown of malicious repositories.
Guidance for the Crypto Community
Fireblocks has stated that it coordinated with intelligence partners and law enforcement to reduce the risk of follow-on attacks. The company, which reports securing more than $10 trillion in digital asset transfers across hundreds of millions of wallets, emphasized the importance of vigilance during recruitment processes.
Job seekers in the crypto sector are advised to verify recruiter outreach against official company career pages and ensure that communications originate from verified corporate email addresses. Fireblocks also noted that being asked to clone repositories and run installation commands as part of an interview process should be treated with caution, even when the overall interaction appears legitimate.
The post Fireblocks Exposes Sophisticated Lazarus-Linked Hiring Scam appeared first on CoinTrust.
You May Also Like
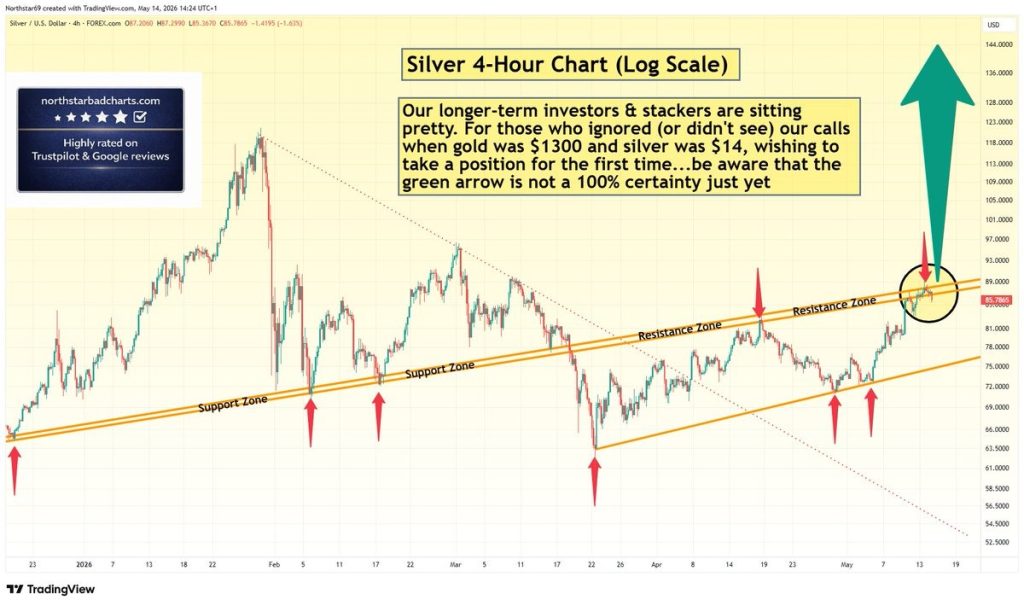
Silver Price Warning: Green Arrow Setup Is Not Confirmed – Wait for Clear Signal

Facebook spotlights African cinema in 6th ‘Made by Africa, loved by the world’ campaign






