Revolutionary KRW Stablecoin Alliance: CertiK and Wemade Forge Global Partnership
BitcoinWorld
Revolutionary KRW Stablecoin Alliance: CertiK and Wemade Forge Global Partnership
Imagine a world where digital currencies mirror real-world stability—that’s the vision behind the groundbreaking KRW stablecoin alliance. CertiK and Wemade just announced their partnership to launch the Global Alliance for KRW Stablecoin (GAKS), a move set to reshape blockchain security and reliability. This collaboration brings together industry giants like Chainalysis and SentBe, focusing on creating a robust infrastructure for won-pegged stablecoins. If you’re invested in cryptocurrency’s future, this development promises enhanced transparency and trust.
What Makes the KRW Stablecoin Alliance a Game-Changer?
The GAKS initiative centers on StableNet, a dedicated blockchain mainnet developed by Wemade specifically for KRW stablecoin operations. As a member, CertiK will conduct thorough security audits and provide a block explorer to boost transparency. This means every transaction becomes traceable and secure, addressing common concerns in the crypto space. Moreover, the alliance plans to establish a long-term framework for technical support and core infrastructure, ensuring the KRW stablecoin ecosystem remains resilient against threats.
How Will This Partnership Benefit Users?
Users stand to gain significantly from this alliance. First, security audits by CertiK reduce risks of hacks or fraud, building confidence in KRW stablecoin transactions. Second, the block explorer allows real-time tracking, making the system more accountable. Here are key benefits:
- Enhanced Security: Regular audits protect against vulnerabilities.
- Improved Transparency: Public access to transaction data fosters trust.
- Global Reach: Partnerships with firms like Chainalysis enable cross-border efficiency.
Therefore, whether you’re a trader or developer, this infrastructure supports smoother, safer operations.
What Challenges Does the KRW Stablecoin Face?
Despite the excitement, challenges exist. Regulatory hurdles in different countries could slow adoption, and market volatility might affect the peg to the Korean won. However, the alliance’s focus on collaboration and technical excellence helps mitigate these issues. By pooling resources, GAKS aims to navigate obstacles and set new standards for stablecoins worldwide.
Why Should You Care About This Development?
This alliance isn’t just about technology—it’s about building a foundation for future financial systems. The KRW stablecoin initiative demonstrates how blockchain can bridge traditional finance and digital assets, offering stability in a often unpredictable market. As more players join, we can expect innovations that make cryptocurrencies accessible to everyone.
In summary, the CertiK and Wemade partnership marks a pivotal moment for KRW stablecoins, combining security, transparency, and global cooperation. This effort not only strengthens trust in digital currencies but also paves the way for broader adoption. Keep an eye on GAKS as it evolves; it could redefine how we think about money.
Frequently Asked Questions
What is a KRW stablecoin?
A KRW stablecoin is a digital currency pegged to the South Korean won, designed to maintain a stable value compared to traditional money.
Who are the members of GAKS?
The alliance includes CertiK, Wemade, Chainalysis, and SentBe, all working together to enhance the KRW stablecoin ecosystem.
How does CertiK contribute to the alliance?
CertiK provides security audits and a block explorer for StableNet, ensuring the infrastructure is secure and transparent.
What is StableNet?
StableNet is a blockchain mainnet developed by Wemade specifically for operating won-pegged stablecoins, offering a dedicated environment for transactions.
Why is transparency important for stablecoins?
Transparency builds user trust by allowing verification of transactions and reducing the risk of fraud or manipulation.
Can this alliance impact global cryptocurrency markets?
Yes, by setting higher standards for security and cooperation, it could influence how stablecoins are developed and regulated worldwide.
If you found this article insightful, share it on social media to spread the word about this exciting advancement in blockchain technology!
To learn more about the latest cryptocurrency trends, explore our article on key developments shaping stablecoin adoption and institutional integration.
This post Revolutionary KRW Stablecoin Alliance: CertiK and Wemade Forge Global Partnership first appeared on BitcoinWorld.
Potrebbe anche piacerti

Tether Backs Ark Labs’ $5.2 Million Bet on Bitcoin’s Stablecoin Revival
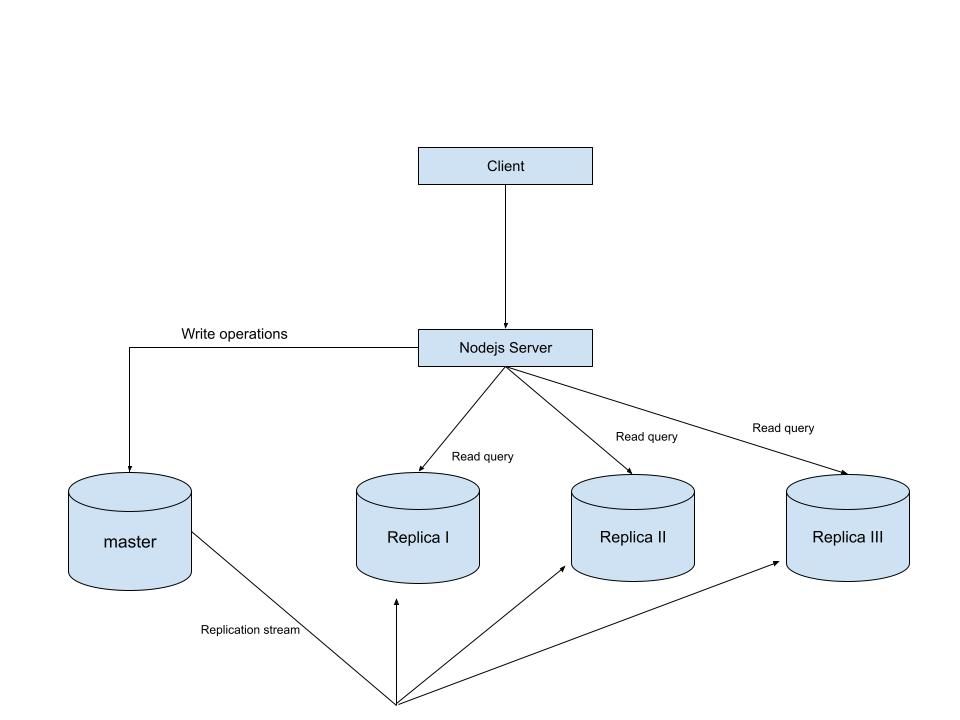
MySQL Single Leader Replication with Node.js and Docker
command: --server-id=1 --log-bin=ON The --server-id option gives each MySQL server in your replication setup its own name tag. Each one has to be unique and without it, replication won’t work at all. Another cool option not included here is binlog_format=ROW. This tells MySQL how to keep track of changes before passing them along to the replicas. By default, MySQL already uses row-based replication, but you can explicitly set it to ROW to be sure or switch it to STATEMENT if you’d rather log the actual SQL statements instead of row-by-row changes. \ Run our containers on docker Now, in the terminal, we can run the following command to spin up our database containers: docker-compose up -d \ Setting Up Our Master (Primary) Server To configure our master server, we would have to first access the running instance on docker using the following command docker exec -it mysql-master bash This command opens an interactive Bash shell inside the running Docker container named mysql-master, allowing us to run commands directly inside that container. \ Now that we’re inside the container, we can access the MySQL server and start running commands. type: mysql -uroot -p This will log you into MySQL as the root user. You’ll be prompted to enter the password you set in your docker-compose.yml file. \ Next, we need to create a special user that our replicas will use to connect to the master server and pull data. Inside the MySQL prompt, run the following commands: \ CREATE USER 'repl_user'@'%' IDENTIFIED BY 'replication_pass'; GRANT REPLICATION SLAVE ON . TO 'repl_user'@'%'; FLUSH PRIVILEGES; Here’s what’s happening: CREATE USER makes a new MySQL user called repl_user with the password replication_pass. GRANT REPLICATION SLAVE gives this user permission to act as a replication client. FLUSH PRIVILEGES tells MySQL to reload the user permissions so they take effect immediately. \ Time to Configure the Replica (Secondary) Servers a. First, let’s access the replica containers the same way we did with the master. Run this command in your terminal for each of the replica containers: \ docker exec -it <replica_container_name> bash mysql -uroot -p <replica_container_name> should be replace with the name of the replica container you are trying to setup b. Now it’s time to tell our replica where to get its data from. While inside the replica’s MySQL shell, run the following command to configure replication using the master’s details: CHANGE REPLICATION SOURCE TO SOURCE_HOST='mysql-master', SOURCE_USER='repl_user', SOURCE_PASSWORD='replication_pass', GET_SOURCE_PUBLIC_KEY=1; With the replication settings in place, let’s fire up the replica and get it syncing with the master. Still inside the MySQL shell on the replica, run: START REPLICA; This starts the replication process. To make sure everything is working, check the replica’s status with:
SHOW REPLICA STATUS\G; Look for Replica_IO_Running and Replica_SQL_Running — if both say Yes, congratulations! 🎉 Your replica is now successfully connected to the master and replicating data in real time.
Testing Our Replication Setup from the Node.js App Now that our replication is successfully set up, we can configure our Node.js server to observe the real-time effect of data being replicated from the master server to the replica server whenever we write to it. We start by installing the following dependencies:
npm i express mysql2 sequelize \ Now create a folder called src in the root directory and add the following files inside that folder connection.js, index.js and model.js. Our current directory should look like this We can now set up our connections to our master and replica server in the connection.js file as shown below
const Sequelize = require("sequelize"); const sequelize = new Sequelize({ dialect: "mysql", replication: { write: { host: "127.0.0.1", username: "root", password: "master", database: "replicaDb", }, read: [ { host: "127.0.0.1", username: "root", password: "slave", database: "replicaDb", port: 3307 }, { host: "127.0.0.1", username: "root", password: "slave", database: "replicaDb", port: 3308 }, { host: "127.0.0.1", username: "root", password: "slave", database: "replicaDb", port: 3309 }, ], }, }); async function connectdb() { try { await sequelize.authenticate(); } catch (error) { console.error("❌ unable to connect to the follower database", error); } } connectdb(); module.exports = { sequelize, }; \ We can now create a User table in the model.js file
const {DataTypes} = require("sequelize"); const { sequelize } = require("./connection"); const User = sequelize.define("User", { name: { type: DataTypes.STRING, allowNull: false, }, email: { type: DataTypes.STRING, unique: true, allowNull: false, }, }); module.exports = User \ and finally in our index.js file we can start our server and listen for connections on port 3000. from the code sample below, all inserts or updates will be routed by sequelize to the master server. while all read queries will be routed to the read replicas.
const express = require("express"); const { sequelize } = require("./connection"); const User = require("./model"); const app = express(); app.use(express.json()); async function main() { await sequelize.sync({ alter: true }); app.get("/", (req, res) => { res.status(200).json({ message: "first step to setting server up", }); }); app.post("/user", async (req, res) => { const { email, name } = req.body; let newUser = await User.build({ name, email, }); // This INSERT will go to the write (master) connection newUser = newUser.save({ returning: false }); res.status(201).json({ message: "User successfully created", }); }); app.get("/user", async (req, res) => { // This SELECT query will go to one of the read replicas const users = await User.findAll(); res.status(200).json(users); }); app.listen(3000, () => { console.log("server has connected"); }); } main(); When you make a POST request to the /users endpoint, take a moment to check both the master and replica servers to observe how data is replicated in real time. Right now, we are relying on Sequelize to automatically route requests, which works for development but isn’t robust enough for a production environment. In particular, if the master node goes down, Sequelize cannot automatically redirect requests to a newly elected leader. In the next part of this series, we’ll explore strategies to handle these challenges
